🔐Protecting Your Application from Clickjacking Attacks in Node.js Express
Bài đăng này đã không được cập nhật trong 2 năm
Clickjacking is a type of security vulnerability that tricks users into clicking on hidden elements on a web page, allowing attackers to perform unauthorized actions on the user's behalf. This article will provide an in-depth look at clickjacking attacks and offer detailed guidance on how to protect your Node.js Express applications from them.
What is Clickjacking?
Clickjacking, also known as UI redressing, is a technique used by attackers to deceive users into performing unintended actions on a website or application. These attacks are accomplished by overlaying hidden elements, such as buttons or links, on top of seemingly innocuous web page elements. As a result, users are misled into interacting with the hidden elements, giving attackers the ability to exploit their actions.
The Impact of Clickjacking Attacks
Clickjacking can lead to various negative consequences, such as:
- Unauthorized actions: Attackers may hijack users' accounts and perform unauthorized actions, like changing passwords or updating personal information.
- Data theft: Attackers can use clickjacking to trick users into revealing sensitive information, such as login credentials, credit card details, or social security numbers.
- Phishing: Clickjacking can be employed as part of a phishing campaign, leading users to believe they are interacting with a legitimate site while actually providing their information to attackers.
Understanding the Node.js Express Framework
Node.js Express is a popular web application framework for building fast and scalable applications. It provides a robust set of features and simplifies the process of creating server-side web applications. However, like any technology, it is crucial to take security measures to protect your applications from potential threats, including clickjacking attacks.
Techniques to Prevent Clickjacking in Node.js Express
1. Implementing the X-Frame-Options Header
The X-Frame-Options header is a security feature that prevents a web page from being embedded within an iframe or frame, which is often used in clickjacking attacks. By setting the X-Frame-Options header, you can restrict your web pages from being embedded in other sites, mitigating the risk of clickjacking.
To implement the X-Frame-Options header in your Node.js Express application, follow these steps:
- Install the
helmetmiddleware:
npm install helmet
- Import the
helmetpackage and use it as middleware in your application:
const express = require('express');
const helmet = require('helmet');
const app = express();
app.use(helmet());
- Configure the X-Frame-Options header using the
frameguardmethod:
app.use(helmet.frameguard({ action: 'deny' }));
The action parameter can be set to 'deny', 'sameorigin', or 'allow-from':
- '
deny': Prevents the page from being embedded within any iframe or frame. - '
sameorigin': Allows the page to be embedded only by the same domain. - '
allow-from': Specifies a list of domains that are allowed to embed the page.
2. Applying Content Security Policy (CSP)
Content Security Policy (CSP) is a security feature that allows you to define a set of rules to control which resources can be loaded by a web page. By configuring a strict CSP, you can prevent unauthorized resources from being loaded, effectively mitigating clickjacking attacks.
To apply CSP in your Node.js Express application, follow these steps:
- Install the
helmetmiddleware if you haven't already:
npm install helmet
- Import the
helmetpackage and use it as middleware in your application:
const express = require('express');
const helmet = require('helmet');
const app = express();
app.use(helmet());
- Configure the Content Security Policy using the
contentSecurityPolicymethod:
app.use(
helmet.contentSecurityPolicy({
directives: {
defaultSrc: ["'self'"],
frameAncestors: ["'none'"],
},
})
);
In the example above, the defaultSrc directive is set to 'self', allowing resources to be loaded only from the same origin. The frameAncestors directive is set to 'none', preventing the page from being embedded within any iframe or frame.
You can further customize the CSP directives according to your application's needs. For example, you can allow specific domains to load resources or embed your pages by modifying the defaultSrc and frameAncestors values.
3. Employing JavaScript Frame Busting Techniques
Frame busting is a technique used to prevent a web page from being embedded within an iframe or frame by using JavaScript code to break out of the frame. Although this method is less reliable than using the X-Frame-Options header or CSP, it can serve as an additional layer of protection against clickjacking attacks.
Add the following JavaScript code to the <head> section of your HTML pages:
<script>
if (top !== self) {
top.location = self.location;
}
</script>
This code checks if the current window (self) is not equal to the topmost window (top). If the condition is true, it means the page is embedded within an iframe or frame, and the script will navigate the topmost window to the current page's location, effectively breaking out of the frame.
Conclusion
Clickjacking is a serious security threat that can lead to unauthorized actions, data theft, and phishing attacks. Protecting your Node.js Express applications from clickjacking requires implementing security measures such as the X-Frame-Options header, Content Security Policy, and JavaScript frame busting techniques. By employing these methods, you can significantly reduce the risk of clickjacking attacks and keep your users' data safe.
Mình hy vọng bạn thích bài viết này và học thêm được điều gì đó mới.
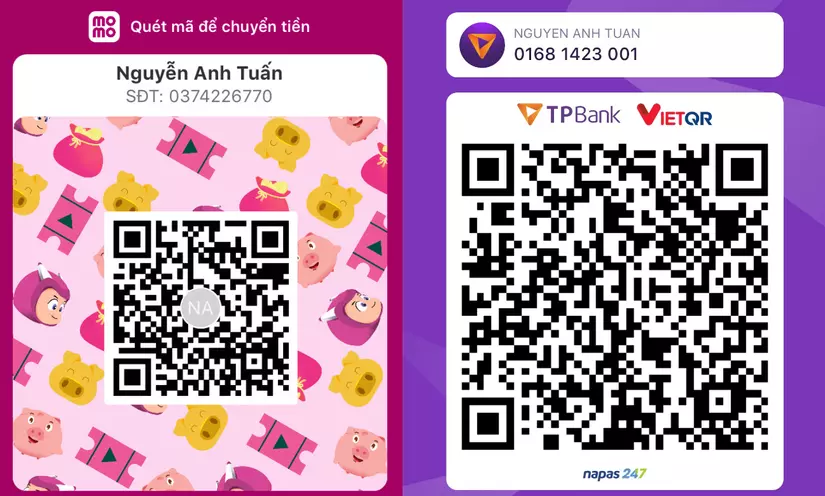
Donate mình một ly cafe hoặc 1 cây bút bi để mình có thêm động lực cho ra nhiều bài viết hay và chất lượng hơn trong tương lai nhé. À mà nếu bạn có bất kỳ câu hỏi nào thì đừng ngại comment hoặc liên hệ mình qua: Zalo - 0374226770 hoặc Facebook. Mình xin cảm ơn.
Momo: NGUYỄN ANH TUẤN - 0374226770
TPBank: NGUYỄN ANH TUẤN - 0374226770 (hoặc 01681423001)
All rights reserved