🔐Preventing Cross-Site Request Forgery (CSRF) Attacks in Express
Bài đăng này đã không được cập nhật trong 2 năm
Introduction to Cross-Site Request Forgery (CSRF) Attacks
Cross-Site Request Forgery (CSRF) is a security vulnerability that allows an attacker to trick a user into performing unwanted actions on a web application, without their consent. In a CSRF attack, the user's browser is used as a conduit for unauthorized requests to a vulnerable application, effectively exploiting the user's authenticated session.
The Importance of Protecting Against CSRF Attacks
If a web application is not protected against CSRF attacks, it can lead to serious consequences, including:
- Unauthorized data modification or deletion
- Unauthorized account access or password changes
- Unauthorized financial transactions
To keep your Node Express applications secure, it's essential to implement proper CSRF protection measures.
Implementing CSRF Protection in Express
In this article, we'll walk through the process of implementing CSRF protection for a Node Express web application, using the following steps:
- Installing necessary packages
- Setting up middleware
- Generating CSRF tokens
- Validating CSRF tokens
- Handling token errors
Step 1: Installing Necessary Packages
First, you'll need to install two packages to help implement CSRF protection: csurf and cookie-parser. To do this, run the following command in your terminal:
npm install csurf cookie-parser
Step 2: Setting Up Middleware
After installing the packages, you'll need to set up the middleware in your Express.js application. Import the csurf and cookie-parser packages and add them to your middleware stack:
const express = require('express');
const cookieParser = require('cookie-parser');
const csrf = require('csurf');
const app = express();
app.use(cookieParser());
app.use(csrf({ cookie: true }));
Step 3: Generating CSRF Tokens
Next, you need to generate CSRF tokens for each user session. To do this, include the csrfToken function in your route handlers:
app.get('/form', (req, res) => {
const csrfToken = req.csrfToken();
res.render('form', { csrfToken });
});
Include the generated CSRF token as a hidden field in your HTML forms:
<form action="/submit" method="POST">
<input type="hidden" name="_csrf" value="{{csrfToken}}">
<!-- other form fields go here -->
<button type="submit">Submit</button>
</form>
Step 4: Validating CSRF Tokens
The csurf middleware automatically validates the CSRF tokens in incoming POST requests. If the token is valid, the request will proceed as normal. If the token is missing or incorrect, an error will be thrown.
Step 5: Handling Token Errors
To handle CSRF token errors gracefully, you can add a custom error handler to your Express.js application:
app.use((err, req, res, next) => {
if (err.code === 'EBADCSRFTOKEN') {
// CSRF token validation failed
res.status(403).send('Invalid CSRF token.');
} else {
// Pass the error to the next middleware
next(err);
}
});
This will catch CSRF token errors and return a 403 Forbidden response with a helpful message.
Conclusion
By following these steps, you can effectively protect your Nodejs Express web applications from Cross-Site Request Forgery attacks. Remember to keep your packages up-to-date and monitor your application's security regularly to ensure that it remains safe from vulnerabilities.
Mình hy vọng bạn thích bài viết này và học thêm được điều gì đó mới.
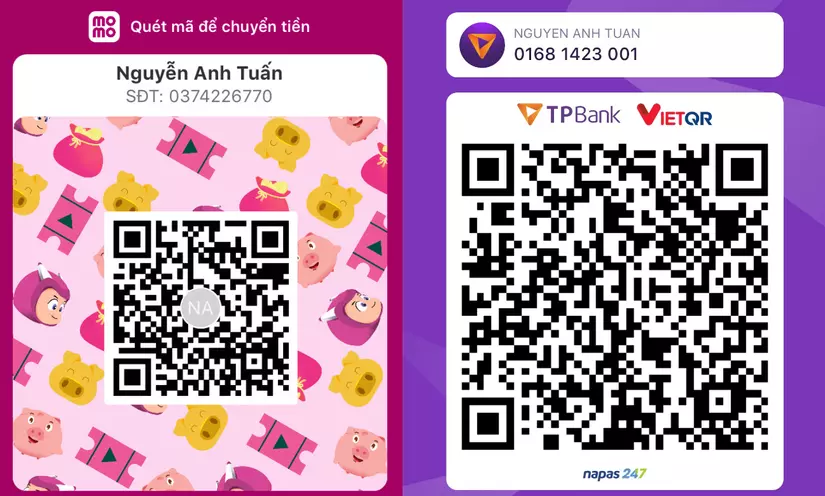
Donate mình một ly cafe hoặc 1 cây bút bi để mình có thêm động lực cho ra nhiều bài viết hay và chất lượng hơn trong tương lai nhé. À mà nếu bạn có bất kỳ câu hỏi nào thì đừng ngại comment hoặc liên hệ mình qua: Zalo - 0374226770 hoặc Facebook. Mình xin cảm ơn.
Momo: NGUYỄN ANH TUẤN - 0374226770
TPBank: NGUYỄN ANH TUẤN - 0374226770 (hoặc 01681423001)
All rights reserved